Table of Contents
How to keep your computer clean?
Security Steps That Can Secure Your Windows-Based Computer From Harm – If Windows is not working correctly, you need to reinstall Windows or have your computer serviced. To leave it to someone who has more experience and knowledge. Before that, copy the files to an external drive or USB. If you use an email client, export the settings and messages to save them. Also, back up your drivers using apps if you don’t want to download them again. Once you have backed up everything you need, you can reinstall Windows. If you visit suspicious sites, you can protect yourself by running an Internet browser in sandbox mode (this prevents malware from harming the system). Check your online accounts (bank accounts, email, and social networks) and focus on suspicious activity. If you notice them, change your passwords because cybercriminals can access them using certain malware.
If you are using automatic file backup, scan them as well to make sure that an infected file is not accidentally saved. Keep all your applications, including Windows, up to date. It is best to set the option to automatically update systems and applications, wherever possible.
Defragmentation is the process by which data on a hard disk is stacked so that the OS and programs can access it as quickly as possible. We all have some files on our computer that are important to us and that we don’t want to lose. File loss can occur due to hard drive crashes, virus attacks, etc. One of the most efficient ways to save and protect your data is to transfer it and save it on external devices.
Update the programs you use to the latest versions: For security reasons, and to make your computer work better, always try to use the latest versions of all programs.
Clean your computer of dust: Each computer fills with dust over time, causing it to overheat. In the worst case, computer overheating caused by dust can cause certain components to fail. To avoid this scenario, take your computer to a service center for cleaning at least once a year, and ideally every 6 months. We do not recommend that you clean your computer from dust yourself, if you are not sure what and how you are doing, you can very easily do more harm than good.
The importance of password managers in protecting against attacks
Password managers have become mandatory for computer users who want to be protected. The master password is essential and represents the key to storing the program. All passwords are stored in one place. These products use powerful encryption with almost unbreakable essential key lengths to protect the safe. Such a database can only be unlocked with the correct master password. So, the user does not need to remember the password for each of his accounts, but only the master password, which is opened with all other codes.
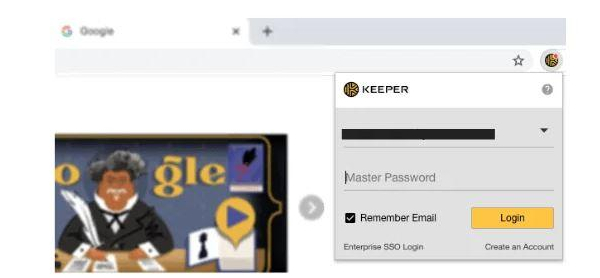
You only need to enter the login password and the master password to start the synchronization. All password managers offer auto-complete credentials in the browser to enter the page. Here is the easiest way to copy and paste the data into the appropriate fields. Android, unlike iOS, makes this easier.
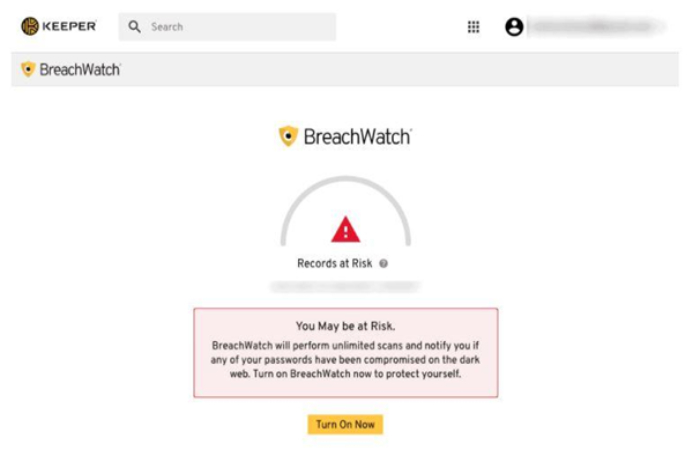
Programs called password managers are generally divided into several main types and allow you to perform many operations to create a store, and organize a huge amount of personalized confidential data with a fairly high degree of protection. Keeper Password Manager is a prime example of that kind of a security tool. The uniqueness of such programs in recent years is increasingly reflected in the fact that some web resources do not store personal passwords, credit card access codes, or register accounts on the computer’s hard drive.
Creating a secure password
Creating passwords is a skill these days. Each of us handles a large number of passwords and that is why we often neglect to make an effort to use secure passwords. A strong password implies a series of letters, numbers, and characters that are made so that there is a high probability that the fastest machine will not be able to hit it within a reasonable time. On the other hand, a strong password is also through letters, numbers, and signs that even a person who knows us best would not be able to guess in a reasonable course of time.

Never use the same code for important accounts: this includes general codes for computer and mobile phones, email accounts, social media accounts, all accounts that reveal financial information (bank, online shopping). All these passwords must be different from each other and all other passwords you use (forums, websites, etc.). Develop your system of words that you use that is diverse enough, but which you can easily remember. If you are an ardent fan of a club or adore a band, don’t use their names. Do not use passwords that are given anywhere as examples of strong passwords. Remember: for your memory and as a security measure, a password that is unique to you is harder to detect through random guessing. Do not use information about yourself that is easy to reveal, for example, date of birth, as well as dates of birth of parents or children, name of a pet, favorite band or sports team, names of brothers, sisters, or children. Rule: If something exists as data or an incidentally mentioned fact on your social media accounts, do not use it as a basis for your password.
The Internet today and the development of the Internet
One of the basic characteristics of today’s age is the growing number of information that comes from different sources such as the daily press, TV, propaganda material, or the Internet. On the one hand, a large amount of that information enabled the ever faster development of human society and on the other hand, it required additional technical aids that are all the same information should be memorized, sorted, and presented promptly.
Huge speed, easy availability, manipulativeness, and the virtually unlimited storage possibilities that the Internet provides, open up unprecedented possibilities for the most diverse use of new technologies that have enabled man to make a large number of quick, complete, and comprehensive decisions. U In that sea of information, it is inconceivable that anyone can manage without the existence of information systems. However, to be able to achieve all this, and in addition to the opportunities provided by information technology, it is necessary to fulfill appropriate preconditions for its efficient functioning. On the one hand, computers have brought many benefits, but they jeopardize some of our most important values, such as security, functionality, and data privacy.

